Claude Mythos and the Machine-Speed Security Reset
Published
Modified
Claude Mythos marks a new machine-speed era in cybersecurity It exposes how much weak software still underpins the digital economy The article argues that firms and policymakers must adapt fast

In April 2026, the UK AI Security Institute found that Mythos could successfully complete all expert hacking tasks 73% of the time, compared to 0% before April 2025. That is the number that counts. That is what matters. That is more important than the speculation or the hysteria. Mythos does not demonstrate AI can break into any existing system, but it does show the baseline for security testing has changed at an alarming rate. Mythos is not just another smart chatbot with a cyber trick; it is a wake-up call, that a new hyper-speed phase of software-based defense is upon us, one driven by the machine hardware itself, long historical context and near-infinite retry potential. For years, cyber planning has characterized AI as just another resource on a depleted market for talent. Mythos suggests the more relevant question is not whether humans will use AI in security more effectively, but whether the systems they are trying to protect will even survive a machine-speed attempt with vast, context-rich codebases and near-perpetual assault attempts.
Mythos confirms cyber knowledge is becoming an all-purpose AI skill
That's why Mythos matters. Unlike dedicated offensive cybersecurity agents, its cyber skill doesn't rest on a specialized purpose: the model is generalist, designed to be an expert in a broad range of reasoning, coding and autonomous tasks. This is the factor that super-charges the model beyond over-hyped "dangerousness". As cyber expertise becomes a meta-goal of AI capability, the idea of offensive security as a detached niche begins to fall away. A system that can effortlessly scan code, analyze dependencies, produce missing context and patiently execute extended attack workflows is already touching the core skills required for advanced vulnerability research. Therefore, Mythos is a borderline case where a state-of-the-art general AI model immediately translates into a tangible impact on mission-critical infrastructure without the need for any domain-specific tool.
This is why the real significance of Mythos isn't merely that it is a scary product launch: its importance is in how it reorients the risk landscape. According to Anthropic, during their audit, Mythos proved capable of cracking zero-day exploits in every major OS and browser they tested, uncovering holes that had gone unnoticed for decades. While their previous model could exploit one Firefox engine vulnerability in hundreds of rounds, Mythos went from 0 to 181 examples, with 29 defenses simulated. Anthropic estimates thousands of such zero-days are out there. If we forget the corporate dogma, the pattern is persuasive. It's not that AI is perfect, but rather that it is getting faster. When security expertise can become a system characteristic, we should expect that general model capabilities will give rise to unforeseen effects on security controls faster than you can say "zero-day".
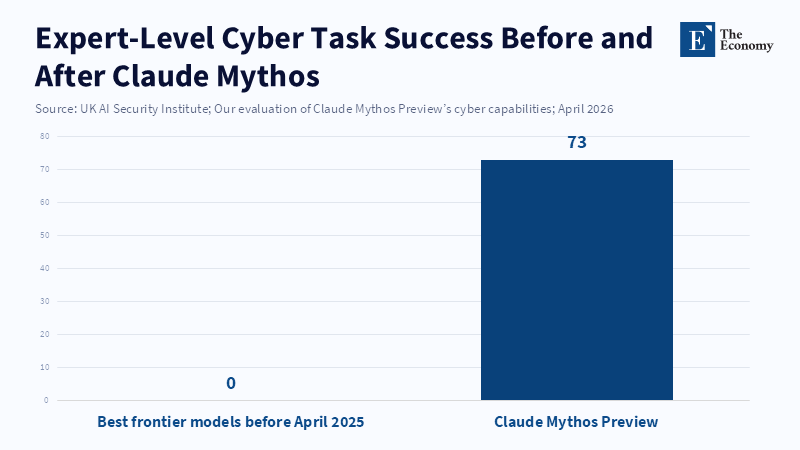
Figure 2
Mythos is changing the economics of unstable code
For years, digital security adopted the soft consensus that vulnerabilities are unavoidable and all discoverability is a function of human limitations; that we humans are the security bottleneck. Mythos undermines that consensus: the security problem becomes less a lament about a lack of manually-capable actors and more about an inventory of susceptibility. When an AI can examine hours of code, predict interactions, reverse engineer binaries and retry exploit after exploit for as long as the attacker wants, the traditional advantage of being able to hide a bug in depth is dramatically reduced. What was a reasonable tech debt threshold when humans are limited now looks like a gaping attack vector when machines are unlimited.
That's why the real concern Mythos should generate for executives, not just red team operators, is that the challenge is no longer that AI will out-expert any individual security analyst, but rather whether your organizational focus has ever really been on reducing "cost of software" over time or whether by necessity you're trying to tolerate software that's just a little more expensive to attack than it is to defend against. According to 2024 IBM research, the average expense of a USA data breach was $4.88mnyet more consumers than ever before were changing providers and 70% of breached firms experienced major or moderate interruptions. All this predates Mythos. Regulators, banking authorities and prosecutors are acting as though the threat isn't in a laboratory, so Norbert's paradox, that better hackers are the best measure of good cybersecurity, applies: more investments in speedier technical response are needed, even before the next models are out there.
Mythos doesn't just change the employment picture; it refocuses what is valuable
It's tempting to say Mythos will reduce the need for any entry-level security specialists. That's probably false. Simple triage, exploit confirmation and segmentation analysis will undoubtedly be automated or significantly improved, but the more important consequence is that the security workforce will shift its emphasis to validation, correction, mitigation and system design. When engineers have no choice but to lean on the tools to identify hundreds of potential weaknesses, the focus pivots from recognizing the problems to fixing the problems and designing them out of the system in the first place. This creates a need for code reviewers and security-focused system engineers, while traditional security employees will find that they need to be more specialized and harder to replace than ever. There are implications for capital investment and for employee choice. The faster security labor moves to the top of the value chain, the faster it will also move to the door for those who are slow.
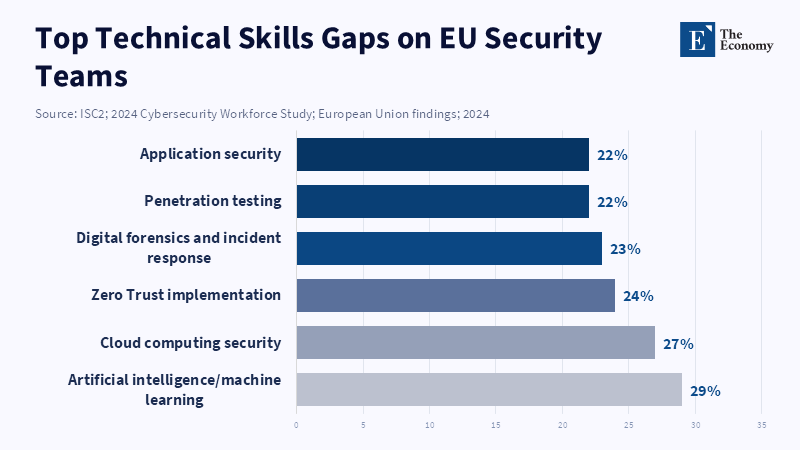
This isn't just obvious from the data about the labor market. The Future of Jobs survey listed AI and big data skills as the fastest-growing occupations among 1,000+ UK firms employing over 14M+ workers, with cyber security in position 3. According to that same report, a skills shortfall in these areas was the No. 1 obstacle to change. The 2024 ISC2 cyber workforce study revealed 1.4M exploits 5.5M cybersecurity workers, leaving a known shortfall of 4.8 M, ample room for them to chase in the European data, where 89% of respondents report talent gaps, with AI/ML a common mention. Claude Mythos accentuates this dynamic: it doesn't make great security expertise redundant; it makes uncovering bad expertise much easier. It also clarifies the message for educators: there's little point in teaching new workers how to rely on old skills, so that they can recognize what good system architecture looks like.
Claude Mythos should evoke policy, not hype: resilience, not spectacle
It's true that Mythos may be an exaggeration, just a special-purpose shopfront in a narrowed universe of capability. There is reason to take this possibility seriously. According to the UK's AI Security Institute, Claude Mythos can succeed in small, quick-responding enterprises, but only after the attacker has already established network footholds: the authors have not claimed the model can reliably out-cyber defenses that actively monitor security events and command elevated privileges by itself. This should be cold comfort: most of the planet's digital infrastructure is exactly these kinds of poorly-secured, unfixed, too-within-budget packages that advanced hackers are actively seeking to compromise. Small providers, hospitals, municipal services, third-tier logistics firms and aging industrial firms don't need time-travel apocalypse attacks. They need to be able to defend faster than an AI-infested botnet can eat them. And they don't need to do it alone yet.
That is why this version of Mythos cannot be considered a sustainable solution. Mythos is not commercially available, but it's certainly not limited to the exclusive world of Alpha-breed corporations. Anthropic continues to see this as a historic trend, not an isolated product. Top-tier talent will be attracted to these model capabilities by its use cases rather than by its function. And the UK's AI Security Institute observed that machine speed improved its performance as more and more tokens piled into its budget. Less than a week after Mythos came out, OpenAI announced an even more advanced cyber-attack model. That trend won't favor the responsible actor. With an undeniable advantage for speed of attack, more and more organizations and nations will make the minimum investment necessary to begin protecting their digital assets. Controls on access won't be enough; policies must develop plans for institutional capacity-building so security vendors and governments are able to keep pace with everyone else.
What then should occur? Neither panic nor apathy. A resilience-first approach that recognizes software quality as a strategic asset. Governments should set new rules for procurement that reward security-by-design, order new mandates for criminal liability over insecure software, accelerate patching and interface upgrades and assist vulnerable industries with expanding cyber defenses. Large companies and governments should act as though software exploitability is no longer a process by which only experts can succeed and boost agency-level investment in prep, detection and monitoring, segmentation, system hardening, audit and power-down simulations and even better security by design, before the next generation of models arrives. Software designers should publish performance benchmarks and independent testing rather than banks' license to publicize "trust us". Mythos doesn't represent the death of security, but the death of the tacit consent to produce neglectfully underpowered code. And institutions must plan accordingly.
Mythos should be seen not as exceptional but as emblematic of the new relationship society will need with its software reliance. This kind of model is neither impossible nor magical; it just helps clear the backlog of weak code and weak hardware that too often underpins our economy. It is not just a failure of security but a failure of system design. Human security work is not becoming obsolete; the low-security bargain that tolerated soft targets for years has to go: this is why Mythos demands action. Institutions will need to adapt their operating models for the new era of quick-fire, zero-error cyber capability.
The views expressed in this article are those of the author(s) and do not necessarily reflect the official position of The Economy or its affiliates.
References
AI Security Institute (2026) ‘Our evaluation of Claude Mythos Preview’s cyber capabilities’, 13 April.
Anthropic (2026a) Claude Mythos Preview System Card, 8 April.
Anthropic (2026b) ‘Project Glasswing’, 7 April.
Carlini, N., Cheng, N., Lucas, K., Moore, M., Nasr, M., Prabhushankar, V., Angulu, W.X.H., Ben Asher, E., Bow, J., Bradwell, K., Buchanan, B., Forsythe, D., Freeman, D., Gaynor, A., Ge, X., Graham, L., Guru, K., Lakhani, H., McNiece, M., Mehrara, M., Nichol, R., Pirzada, A., Porter, S., Terzis, A. and Troy, K. (2026) ‘Assessing Claude Mythos Preview’s cybersecurity capabilities’, 7 April.
Criddle, C. (2026) ‘Anthropic’s Mythos AI model tests limits of global cyber defences’, Financial Times, 18 April.
Goldstein, G.M. (2026) ‘Six Reasons Claude Mythos Is an Inflection Point for AI—and Global Security’, Council on Foreign Relations, 15 April.
Gupta, N. (2026) ‘Anthropic’s Claude Mythos and What it Means for Security’, ArmorCode Blog, 14 April.
IBM Security and Ponemon Institute (2024) Cost of a Data Breach Report 2024.
ISC2 (2024a) 2024 ISC2 Cybersecurity Workforce Study, 31 October.
ISC2 (2024b) 2024 ISC2 Cybersecurity Workforce Study: European Union Findings.
McMahon, L. and Tidy, J. (2026) ‘What is Claude Mythos and what risks does it pose?’, BBC News, 17 April.
Murdoch, S., Yang, H., Kok, X., Ngui, Y. and Li, S. (2026) ‘Asia regulators monitor Anthropic’s Mythos for potential banking risks’, Reuters, 20 April.
Newman, L.H. (2026) ‘Anthropic’s Mythos Will Force a Cybersecurity Reckoning—Just Not the One You Think’, WIRED, 10 April.
Sims, T. (2026) ‘German banks examine risks of Anthropic’s Mythos with authorities’, Reuters, 16 April.
Stokel-Walker, C. (2026) ‘What is Mythos, Anthropic’s unreleased AI model, and how worried should we be?’, Scientific American, April.
U.S. Bureau of Labor Statistics (2025) ‘Software Developers, Quality Assurance Analysts, and Testers’, Occupational Outlook Handbook.
World Economic Forum (2025) The Future of Jobs Report 2025, 7 January.