The Scam Centers Are Not the System: Why Southeast Asia’s Voice Phishing Crackdown Still Misses the Core
Authored On
Modified
Scam compounds can be closed, but the network behind them often survives The real test is whether the money, telecom, and command structure are broken Without that, the crackdown stays visible but incomplete

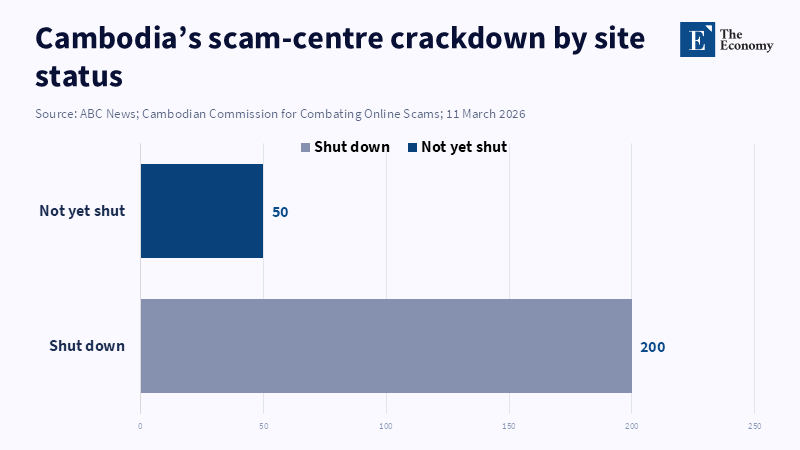
Cambodia says it has shut down about 200 of the roughly 250 sites it believes were offering online scams. Paper, it is all paper. Not that much, in fact. For a cross-border, major voice phishing event, the real operator cannot have a business in which you cut out the lights, clear the compounds, and hang up the police tape. You can't have the owners of the sites, the operators of the sites, the guys who run and keep the sites going, the guys who run the route the calls take, who relay the cash jumps, who keep everything running exactly the same, but in a different country around the corner. No. That is the harder bit, and South East Asia has yet to show it can do it. It is raids, deportations, sanctions, new laws, and repeated assurances to literally annihilate the sites. But the lighted terminal system still exists. It is no longer out on the street. It is still hiding away. Just out of sight. So every new offensive has the feeling of elation and excitement, and a degree of unfinished business about it. Buildings change. Scripts change. Geography changes. The system? It does not.
The voice phishing purge 'is killing websites, not business'
The gravest error at present is to confuse a compound, the worksite, and its huge network of operators. The entire system is very different. Reuters reported on 3 April that Cambodia has finally passed its first piece of legislation to target scam sites, with jail sentences and fines for online scams, money laundering, illegal collection of data, and recruitment. This is important. It offers officials a range of enforcement options, and it also indicates to Phnom Penh that the scam economy can no longer be brushed aside as a matter of no consequence. However, the same Reuters piece also claimed that the formerly sporadic raids have failed to stem the growth of these establishments, even though officials currently claim that a nationwide crackdown shut down hundreds of sites and netted many senior figures. That is the real risk; states can raid an individual compound in a day, but cannot wipe out a cross-border operation made up of funding sources, recruiters, telecom enablers, document forgers, and money launderers, all in one weekend.
These props and remaining evidence are what explain the importance. Reuters found this in Kampot: 'Seeing huge workshop areas lined with rows of computer stations, booths where the scammers took the calls, instructions on how to trick the Thai victims, even a fake police station.' far more detail was uncovered by The Guardian on the O'Smach site: […], fake bank branches, fake police stations, uniforms and badges, scripts, lists of targets and paperwork demonstrating a highly sophisticated business operation in the imitation of officialdom. This was not a mere crime of opportunism but 'a factory mass, production lines designed to sound real, encourage patience to look real, and lead the 'victim' safely into their folder with the real contents.' Indeed, this is the significance behind the central lesson of this article. When a voice phishing raid is considered a success, when the 'steamroller' based on its physical plant is calculated, the physical decoy can be 'put on ice,' and the 'engine room' can move away to reestablish the scam elsewhere.
And this, of course, is why the arrest figures need not be too reassuring. In a Reuters report published in February, Cambodia had rounded up some 173 major criminals, deported about 11,000 workers, and flushed out roughly 190 compounds, all figures. They indicate serious activity. But they do not show a tactical win. Reuters reports also set out the flaws in the operation: in one compound, no arrests had been made "when people had already fled" after the boss had been assessed to have been "taken away," and police also admitted they did not have enough drivers to pursue existing fleeing members. This captured more than the headline. It shows an enterprise that had informants, hit routes, and interchangeable chains of command personnel. The soldiers involved in this type of operation are naturally the most flexible and interchangeable. The real conundrum is whether the topmost tiers of their operation have been fully decrypted, allocated to all possible factions, and divested of the assets, authorizations, and accounts required to make the next compound feasible. That task is still pending.
Why the voice phishing crusade just spurs migration, not brings it to an end
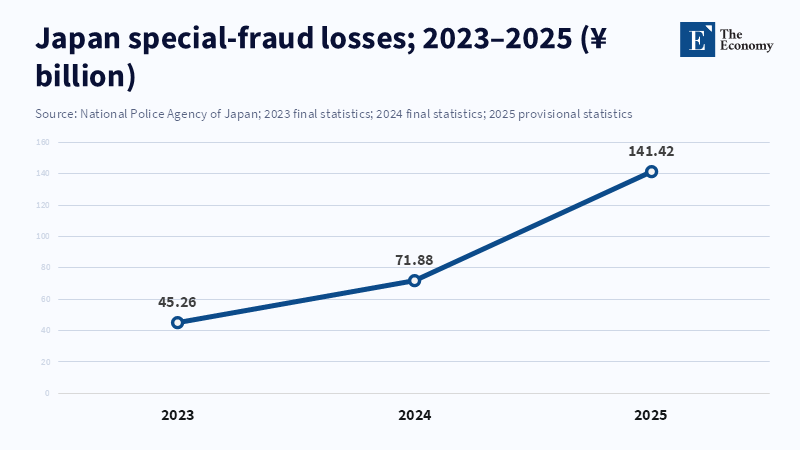
UNODC's 2025 assessment explained why this story keeps happening. Its report found that States were not winning either; no matter what the authorities did, criminals were always working out how to carry on operating. When law enforcement increased in one area, new territories and borderlands sprouted up where the state had less control. UNODC described a global network of mafias with the most skilled drug traffickers, who used the weak State institutions, corrupt officials, and gaps between police and civil authority. It calculated hundreds of high-value fraud offices that conjured up almost US$40 billion per year. That second is huge, and the real point is structural: this is not a criminal tail that can be waged down to a level where a handful of locations could be swept clean; criminal networks are a catastrophe larger than that. If it takes a voice, a phishing attack that cannot eliminate migration to learn how to disable the whole system, so be it.
That is what makes this so difficult to break down. This is what politicizes it. The Guardian's stories about Prince Group and Chen Zhi raised pointed questions about the links between the growth of the scam industry, the property market, the proliferation of business shell companies, and the shielding of the Cambodian elite. Reuters too noted that until recently, Cambodia had played down the presence of scam gangs before launching a wider crackdown. And that history is significant. You would not find a modern industrial system of that scale in isolation from the world; no system that large can survive without land, building, roads, capital, supplies, a paper trail, and a space in which to work. It flourishes where enforcement is patchy, where ownership is obscured, and where the boundaries between good business and criminal service marketing are blurred. That is why, even in this phase, the picture still feels a little patchy. When you identify the major characters, there is still an overwhelming absence of the back office infrastructure; the industry network was largely untraceable, which supported them for so long.
What would be the first step of a real voice phishing stamp out?
A better fight would have to begin way before the raid, with the encalvechets, which facilitate the genesis, the funding, and the linking and monetization of the compounds, too. The ASEAN anti-scams playbook comes close with its 2026 roadmap. It mentions that 80% of scams involve voice calls or SMSs in some member states, and calls to action to reinforce the heart of the scam ecosystem, within it. So if we are to really put the stake in voice phishing, body blow to 419, we have to begin with data sharing over numbered entities, more resilient caller authentication, rapid cross-border identification, upgraded blocking powers, and one plan for all telecoms. But telecoms aren't enough. Cross-border money laundering intelligence units have to weather the way ahead. Beneficial owner info has to be actually available, and not just potentially possible. The freezes have to hit the compounds, and the shell companies, and the cryptocurrency exchanges, and the mule banks, and the service providers that tip the scam economy. Because as long as those links remain, compounds will be situational, raids will be curtain moments.
The second should be framed by the criteria of "success". And today, success appears to be the advertising of closed sites, the detention of workers, and the big police campaigns. Those were good politics, but they are not enough. The real challenge will be to show that prosecutors have been able to nail the whole command structure, to unveil the flows of cash, to break down the front organizations, and to demonstrate the local protection. That is, to show that witnesses can be reasonably safe, trafficked victims are treated as victims, not scapegoats, and that the state can prove that the same operation cannot sneak in, at the same portal, with a different face and enough new life in it to keep it going. The new law in Cambodia may be a beginning, and so might the increasing international pressure underlined by Reuters, including the use of sanctions and extradition to punish senior officials. But the test has to be a measure of success, not activity. And a state should not be given the benefit of the doubt about making the scam economy less noticeable if it has not made it harder for people to do so.
That's the core policy lesson from Southeast Asia and its scare, forecast,filled, boom: not that states have been frozen and helpless in the face of a complex movement, but that policy so often stays focused on the most striking aspect of the system, and takes no other analogies. A shopping mall is a disease, and the network isn't. Until governments regard telecom access, digital movement of financial value, transplanting of labor, protected property, and political cover equally as figures of a single crime model, they will keep confusing reform with zeroing out. Cambodia may have shut down somewhere between 200 of its known 250 sites. That's neither a terrific achievement nor a conclusion. A burbling voice, a phishing campaign begins only when the group of scoundrels is not easier to spot than the buildings they had earlier attended. That's just when it's completed: when the rent is returned to some site to create something new.
The views expressed in this article are those of the author(s) and do not necessarily reflect the official position of The Economy or its affiliates.
References
ASEAN Secretariat (2026) ASEAN Guide on Anti-Scam Policies and Best Practices. Jakarta: ASEAN Secretariat.
Franceschini, I., Bo, M., Li, L. and Loughlin, N. (2026) ‘Southeast Asia’s whack-a-mole scam economy’, East Asia Forum, 9 April.
Lach, C. (2026) ‘Cambodian parliament passes landmark cybercrime law after scam centre scrutiny’, Reuters, 3 April.
Office of the High Commissioner for Human Rights (2026) A “wicked problem”: Seeking human rights-based solutions to trafficking into cyber-scam operations in South-East Asia. Geneva: Office of the High Commissioner for Human Rights.
Ratcliffe, R. (2026) ‘Industrial-scale scams and a state allegedly “co-opted”: What the rise and fall of the Prince group means for Cambodia’, The Guardian, 18 March.
Ratcliffe, R. and Siradapuvadol, N. (2026) ‘Fake rooms, props and a script to lure victims: inside an abandoned Cambodia scam centre’, The Guardian, 14 March.
Reuters Staff (2026) ‘Cambodia says it has closed almost 200 scam centers in fraud crackdown’, Reuters, 11 February.
United Nations Office on Drugs and Crime (2025) Inflection Point: Global Implications of Scam Centres, Underground Banking and Illicit Online Marketplaces in Southeast Asia. Bangkok: United Nations Office on Drugs and Crime.

















